A nation must think before it acts.
Come January 2019, there will be a Democratic majority in the House of Representatives that will simultaneously bring Democratic control to the committees (Judiciary and Intelligence) exercising principal oversight responsibility in the House over foreign intelligence legislation. With several expiring provisions in the Foreign Intelligence Surveillance Act (FISA) up for renewal in 2019, it is not too early to take a look at the issues likely to dominate the reauthorization debate.
But January remains several weeks away, and some of the Republicans who have made FISA a pawn in the fractured politics surrounding the Special Counsel investigation apparently have resolved not to go quietly. Just last week, Bob Goodlatte, the soon to depart chairman of the House Judiciary Committee, announced an intention to subpoena and depose James Comey and Loretta Lynch behind closed doors as part of his Committee’s long-running investigation of alleged bias in the Obama Justice Department and its effect on Justice Department actions during the 2016 election. At this point, it is unclear whether either Comey or Lynch actually will appear, but what is clear is that Goodlatte has run out of time for this new effort to have any material effect on an investigation that will surely lose steam or dramatically change direction once a Democrat (expected to be Jerrold Nadler) assumes the Judiciary chair.
Meanwhile, Devin Nunes who, unlike Goodlatte, will still have a seat in the 116th Congress, continues to agitate for further declassification of classified intelligence documents relating to the Russia investigation and to the four FISA applications and orders that provided the authority to surveil Carter Page during that investigation. Whether or not the president ultimately declassifies all or any part of these materials is a question that may very well linger into 2019, but, come January 3, Nunes will no longer have the chair of the House Intelligence Committee to use as a bully pulpit for his agitprop.
None of this means that the debate that can, and should, accompany consideration of renewing these FISA provisions will be any less spirited, but, perhaps, the focus can be directed to the merits of the legislation rather than devolve into the partisan sniping that, in the House, has dominated Republican “oversight” of intelligence matters for the past year.
Background
While the expiring FISA provisions do not represent legislative authority for an entire collection program as was the case with last year’s debate surrounding the reauthorization of FISA Section 702, they do represent authority for other discrete components added to the FISA framework as part of the legislative response to the September 11 attacks. Two of the provisions originated as amendments enacted as part of the USA PATRIOT Act: section 206 of that Act amended FISA to permit multipoint, or “roving,” wiretaps by adding flexibility to the degree of specificity with which the location or facility subject to electronic surveillance under FISA must be identified; and, section 215 of that same law enlarged the scope of materials that could be sought under FISA to include “any tangible thing,” while also lowering the standard required before a court order may be issued to compel their production.[1] A third amendment, added in 2004, was enacted as part of the Intelligence Reform and Terrorism Prevention Act (IRTPA). Section 6001(a) of the IRTPA changed the rules regarding the types of individuals who may be targets of FISA-authorized electronic surveillance. Colloquially known as the “lone wolf” provision, it permits surveillance of non-U.S. persons engaged in international terrorism without requiring evidence linking those persons to an identifiable foreign power or terrorist organization as is otherwise required in connection with “traditional” FISA surveillance applications.
The 2015 reauthorization of these particular FISA provisions generated significantly more contentious debate following the unauthorized disclosures made by Edward Snowden in June 2013, which, among other things, publicly revealed the existence of the National Security Agency’s (NSA) collection of telephony metadata in bulk. The ensuing controversy precipitated a brief sunset of these three FISA provisions on the then-mandated June 1, 2015 termination date; but, the disruption lasted only until Congress passed, and the president signed, the USA Freedom Act[2] on June 2, 2015 restoring, in modified form, those parts of the Patriot Act which had expired the day before (including the authorities previously embodied in sections 206 and 215). The 2015 reauthorizations included a new sunset date of December 15, 2019 for these particular FISA provisions, setting the stage for a new debate sure to start shortly after the 116th Congress is sworn into office on January 3, 2019. Here is what is at stake for the metadata, roving wiretap, and lone wolf terrorist provisions.
The Collection of “Metadata” under FISA
Thanks in no small part to the publicity surrounding the Snowden disclosures, the most well-known of the three FISA provisions expiring in 2019 relates to the collection of telephony metadata. The USA Freedom Act ended bulk metadata collection and requires that applications seeking the production of Call Detail Records[3]—commonly referred to as “call event metadata”—be approved by the Foreign Intelligence Surveillance Court (FISC).[4]
The specific requirements imposed by the USA Freedom Act mandate a targeted, FISC-approved application in which the government must provide: (1) one or more specific selection term(s)[5] to be used as the basis for production of those tangible things sought by the application; and (2) a statement of facts showing that there are reasonable grounds to believe that the tangible things sought are relevant to an authorized investigation (other than a threat assessment) conducted to obtain foreign intelligence information (not concerning a U.S. person) or to protect against international terrorism or clandestine intelligence activities.[6]
For applications specifically related to authorized international terrorism investigations and seeking call detail records on an ongoing basis, an application’s statement of facts must show there are reasonable grounds to believe that the call detail records sought to be produced based on the specific selection term provided in the application (1) are relevant to such investigation; and (2) that there is a reasonable, articulable suspicion that such specific selection term is associated with a foreign power or an agent of a foreign power engaged in international terrorism.[7]
Upon finding that the application contains the required statutory showing, the FISC “shall enter an ex parte order as requested, or as modified, approving the release of tangible things,” including, where sought in the application, the production of call detail records held by a communications service provider. The order may require the production of call detail records on an ongoing daily basis for a maximum period of 180 days.
As provided with all FISA orders directing the assistance of third parties, no action may be brought in any court against any third party providing assistance to the government in connection with the execution of a FISA order.[8]
In one significant feature, the standards for obtaining call detail records related to an authorized international terrorism investigation are relaxed. Whereas a standard order under FISA Title V (50 U.S.C. § 1861) would generate production only of those records that are responsive to an approved specific selection term, an order seeking call detail records for an international terrorism investigation can also be used to obtain production of a second set of telephone records that, while not themselves responsive to a FISC-approved specific selection term, are connected to one of the records that was directly produced in response to that specific selection term.[9] For example, in a FISA business records application seeking the production of call detail records relating to an international terrorism investigation, if A calls B, and B also calls C, then a single FISC business records production order using A’s phone number as a specific selection term could be used to obtain records not only of the call to B, but also records of the call from B to C. However, as noted, in order to take advantage of this increased scope of production, the government’s FISA application must demonstrate to the FISC a “reasonable articulable suspicion” that the specific selection term included in the application (e.g., the telephone number used with Phone A) is associated with a foreign power, or an agent of a foreign power, engaged in international terrorism.
To elaborate further, assume an NSA intelligence analyst learns that A (the target) is a suspected international terrorist using Phone A. Phone A is the “specific selection term” or “selector” that will be submitted in the application to the FISC while supplying facts demonstrating the “reasonable articulable suspicion” required to connect the selector (i.e., Phone A) to a foreign power or agent of a foreign power engaged in international terrorism. Assume that one communications provider (provider X) submits a record showing that Phone A called another unique identifier (Phone B) (in the parlance of FISA, this is referred to as a “call event”). This connection is what is referred to as the “first hop” in the communication sequence. In turn, assume that the NSA submits the “first-hop” Phone B identifier to provider X, and finds that this unique identifier was used to call another unique identifier, Phone C. The NSA can also seek to have the call detail records associated with this “second-hop” produced.[10]
In practice, the NSA does not directly petition the FISC for call detail records or any other form of business record, nor does it deal directly with telecommunications service providers; instead, all such applications are routed through and handled by the Federal Bureau of Investigation (FBI). Unlike the bulk collection that preceded the changes made by the USA Freedom Act, the NSA’s call detail records program (CDR program) does not routinely collect and hold call detail records at the NSA, and any records now produced pursuant to a FISC order are retained at the NSA only if those records contain foreign intelligence information (as defined in FISA (50 U.S.C. § 1801(e)).
Absent information to the contrary, the NSA presumes that each user of each of the telephone numbers in the above example is a U. S. person where each phone number has a U.S. area code. The NSA’s FISC-approved minimization procedures for the USA FREEDOM Act prohibit the NSA from disseminating any known or presumed U.S. person information that does not constitute foreign intelligence information related to international terrorism or information necessary either to understand foreign intelligence information related to international terrorism or to assess its importance (or where the information is otherwise evidence of a crime). In addition, the minimization procedures require the NSA to destroy promptly any call detail records that are determined not to contain foreign intelligence information. Those minimization procedures also set a maximum retention period for call detail records obtained pursuant to the FISC’s orders of no more than 5 years after initial delivery to the NSA, except that the NSA may retain any call detail record (or information derived therefrom) that was the basis of a properly approved dissemination of foreign intelligence information.
Following the enactment of the USA Freedom Act into law, on November 28, 2015, in compliance with the requirements of that Act, the Intelligence Community terminated collection of bulk telephony metadata with all future production of business records and other tangible things thereafter pursued solely in accordance with the amended requirements of Title V of the FISA.
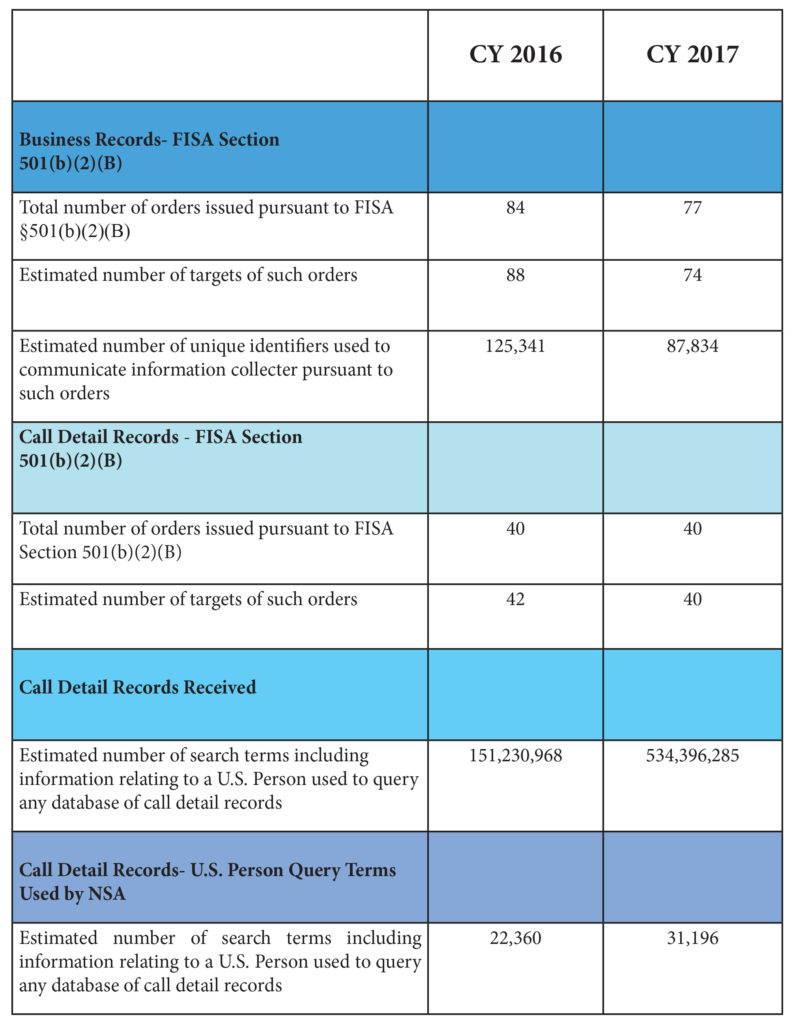
The Director of National Intelligence (DNI) is required to report various statistics about two Title V provisions—traditional business records and call detail records (CDRs). To provide some context for the frequency with which FISA’s provisions governing the production of business records (including CDRs) are used, the DNI’s Statistical Transparency Report for the 2017 calendar year discloses the following[11] metrics.[12]
One additional “counting” caveat from the DNI bears mention. While the FISA statute, as modified by the USA Freedom Act, directs that the government provide a good faith estimate of “the number of unique identifiers used to communicate information collected pursuant to” FISA orders issued in response to applications seeking call detail records (see, 50 U.S.C. §1873(b)(5)(B)), the statistic providing the “Call Detail Records Received” (Table 3) does not reflect the number of “unique” identifiers contained within the call detail records (CDRs) received from providers. The metric in Table 3 (and provided by the DNI’s Statistical Transparency Report) is over-inclusive because the government counts each record separately even if the government receives the same record multiple times (whether from one or multiple providers). The metric also includes duplicates of “unique” identifiers because the government lacks the technical capability to isolate unique identifiers contained within the call detail records received from one or more telecommunications service providers so that the count in Table 3 includes records containing duplicate identifiers. Notwithstanding the caveats offered by the DNI to its statistical presentation, a half billion call detail records for CY 2017 is sure to draw the attention of critics in the forthcoming debate surrounding the reauthorization of metadata collection under FISA.
The “Roving” Wiretap
Section 206 of the USA PATRIOT Act amended FISA to permit multipoint, or “roving,” wiretaps by adding flexibility to the degree of specificity with which the location or facility subject to electronic surveillance under FISA must be identified. It is often colloquially described as allowing FISA wiretaps to target “persons” rather than “places.”
Prior to the enactment of Section 206, the scope of electronic surveillance authorized by a court order was limited in two ways. First, the location or facility that was the subject of surveillance had to be identified. Second, only identifiable third parties could be directed by the government to facilitate electronic surveillance. This was problematic given that conducting electronic surveillance frequently requires the assistance of telecommunications providers, landlords, or other third parties and that telecommunications providers are generally prohibited from assisting in electronic surveillance for foreign intelligence purposes except as authorized by FISA.[13] In cases where the location or facility was unknown, the identity of the person needed to assist in effectuating the government’s surveillance could not be specified in the order, effectively limiting the reach of FISA surveillance to known and identifiable locations.
Section 206 of the USA PATRIOT Act amended Section105(c)(2)(B)[14] of FISA by authorizing FISA orders to direct “other persons” to assist with electronic surveillance if “the Court finds, based on specific facts provided in the application, that the actions of the target . . . may have the effect of thwarting the identification of a specified person.” Then, in a technical amendment passed later in 2001, the requirement that the order specify the location of the surveillance was also changed so that this requirement only applies if the facilities or places are known. These modifications have the effect of permitting FISA orders to direct unspecified individuals to assist the government in performing electronic surveillance, thus permitting court orders to authorize surveillance of places or locations that are unknown at the time the order is issued.
Later amendments required that the FISC be notified within 10 days after “surveillance begins to be directed at any new facility or place.” Additionally, the FISC must be told the nature and location of each new facility or place, the facts and circumstances relied upon to justify the new surveillance, a statement of any proposed minimization procedures that differ from those contained in the original application or order, and the total number of facilities or places subject to surveillance under the authority of the present order.
The Fourth Amendment imposes specific requirements upon the issuance of warrants authorizing searches of “persons, houses, papers, and effects.” One of those mandates, referred to as the “particularity” requirement, states that warrants shall “particularly describ[e] the place to be searched.” Under FISA, roving wiretaps are not required to identify the location that may be subject to surveillance, which raises the question of whether roving wiretaps comport with the particularity requirement of the Fourth Amendment.
Similar roving wiretaps have been permitted under Title III (governing electronic surveillance for law enforcement purposes) since 1986 in cases where the target of the surveillance takes actions to thwart such surveillance.[15] The procedures to obtain a surveillance order under Title III are analogous to those currently used under FISA, but three significant differences exist. First, a roving wiretap under Title III must definitively identify the target of the surveillance while a roving surveillance under FISA need only identify the target if the target’s identity is known.[16] FISA permits roving surveillance via court orders that only provide a specific description, but not necessarily the identity, of the target.[17] Second, some (but not all) roving surveillances in criminal cases are subject to an “ascertainment” requirement mandating that surveillance cannot begin at any particular location or facility until the target’s presence at the location, or use of the facility, is determined or “ascertained.”[18] FISA contains no similar requirement arguably leading to the possibility that a FISC surveillance order might be issued without either the target or facility identified in that order—an anomalous result that critics insist cannot be squared with the Fourth Amendment. Lastly, Title III requires that the surveilled individuals be notified of the surveillance, generally 90 days after surveillance terminates; FISA contains no similar notification provision.
The “Lone Wolf” Terrorist
Commonly referred to as the “lone wolf” provision, Section 6001(a) of IRTPA simplifies the evidentiary standard used to determine whether an individual, other than a U.S. person (as defined in FISA), who engages in international terrorism may be the target of a FISA court order. It does not modify other standards contained in FISA that bear upon the secondary question of whether electronic surveillance or a physical search of the target of a court order is justified in a specific situation.[19]
The historical impetus for the “lone wolf” provision involved Zacarias Moussaoui, alleged at one time to be the 20th hijacker in the September 11 attacks. During the examination of the events leading up to the attacks, it was reported that the investigation regarding Moussaoui’s involvement was hampered by limitations in FISA authorities. Although critics have argued subsequently that nothing in, or missing from, the language of FISA at the time hampered the investigation of Moussaoui requiring any sort of legislative “fix,” Congress responded in IRTPA by providing that persons, other than U.S. persons, engaged in international terrorism are presumptively considered to be agents of a foreign power.[20] The amendment obviates any need for an application seeking surveillance authority and relying on the “lone wolf” provision[21] to provide an evidentiary connection between an individual and a foreign government or terrorist group.
What to Expect in the Coming Legislative Debate
Not surprisingly, the proximity of the Snowden disclosures to the reauthorization process that produced the USA Freedom Act dictated that the NSA’s acquisition and use of bulk telephony metadata dominated the debate. With those disclosures now more remote in time, and having prompted substantial changes in the process by which the NSA accesses and retains metadata, the coming debate might have been expected to be more evenly balanced among the three FISA provisions that, unless extended, will sunset on December 15, 2019.
But, in a paradigm of poor timing, the NSA announced earlier this year that it had begun deleting all (to be read as: “hundreds of millions”) of the call detail records it had acquired since 2015 due to “technical irregularities” in the data received from telecommunications service providers that resulted in the NSA receiving “some CDRs it was not authorized to receive.” When it became clear that the NSA was unable to technically identify and isolate properly produced data, the NSA concluded (in consultation with the DNI and the Department of Justice) to delete all CDRs.[22]
This sort of news is red meat for critics of the NSA’s CDR program and will surely fuel opposition dedicated to eliminating the program or renewing it only with substantial change. Moreover, despite having years to adjust to the new circumstances precipitated by the USA Freedom Act’s passage, the NSA continues to be unable to provide a public estimate of the number of unique identifiers swept up by the program.[23]
These programmatic shortcomings arguably leave Congress and the public unable to evaluate how much the CDR program contributes to security or how broadly the program impacts privacy. Since the privacy intrusion is ostensibly balanced against the CDR program’s contribution to national security, it will be important for the Intelligence Community to demonstrate the program’s continuing value. From the perspective of public debate, this creates a conundrum given that such a showing likely requires some detailing of the program’s contribution to combatting international terrorism—a presentation the details of which will almost assuredly involve highly classified disclosures revealed only in closed session. Consequently, it will be important that Congress, and most particularly the Intelligence and Judiciary Committees in both the House and the Senate, prudently execute their oversight responsibilities—a tasking for which the recent performance of some of these committees has not inspired confidence (although the change in congressional authority in the House offers some hope for improvement).
While less controversial, the “roving wiretap” and “lone wolf” provisions carry their own importance in the toolbox of national security authorities. Each provision, however, stretches (unnecessarily in the view of critics) the constitutional boundaries imposed by the Fourth Amendment. In the case of the roving wiretap, the coming legislative discussion will likely focus on whether congressional “tweaks” are needed to align the FISA requirements more closely with those found in Title III to furnish those checks and balances (e.g., imposing an “ascertainment” requirement) that assure a “reasonable” search under the Fourth Amendment given the lack of “particularity” inherent in any “roving” surveillance.
Similarly, consideration of reauthorizing the “lone wolf” provision in FISA is likely to renew the discussion of whether the provision was ever necessary at all. Largely enacted as a response to purported deficiencies that hampered the FBI’s effort to identify Zacarias Moussaoui as the “20th hijacker,” critics have argued that FISA’s legitimacy is threatened by the definitional illogic of designating a person acting totally alone as “an agent of a foreign power.” Conversely, supporters insist that the evolving and amorphous nature of international terrorism requires that FISA be available as a tool to protect against the multiple, highly splintered threat now posed by terrorists, whether acting alone or in concert. The coming debate may, at times, appear as a byzantine journey into constitutional nuance but, as commentators have warned, the legitimacy of FISA itself may be threatened if its use against a true “lone wolf” is ever challenged in court.[24]
While these upcoming reauthorizations may not implicate what I described last year as “America’s most important intelligence collection program,”[25] the FISA provisions expiring in 2019 are no less likely to prompt serious debate in the new Congress over their continued utility and role in the nation’s national security arsenal.
[1] The FISA provisions related to section 215 of the USA PATRIOT Act are codified in Title V of FISA relating to “Access to Certain Business Records for Foreign Intelligence Purposes” and found at 50 U.S.C. § 1861, et seq.
[2] H.R. 2048, Pub.L. 114–23. The title of the act is a ten-letter acronym (“USA FREEDOM”) standing for the “Uniting and Strengthening America by Fulfilling Rights and Ending Eavesdropping, Dragnet-collection and Online Monitoring” Act.
[3] Now a defined term in FISA, a “call detail record” “means session-identifying information (including an originating or terminating telephone number, an International Mobile Subscriber Identity number, or an International Mobile Station Equipment Identity number), a telephone calling card number, or the time or duration of a call;” but, does not include the contents of any communication, the name, address or financial information of a subscriber or customer, or cell site location or global positioning information. 50 U.S.C. §1861(k)(3).
[4] Applications may be made to one of the eleven FISC judges or to a U.S. Magistrate Judge publicly designated by the Chief Justice to have authority to hear applications and grant orders for the production of tangible things under [50 U.S.C. § 1805]. To date, no U.S. Magistrate Judge has been designated for such purpose.
[5] A “specific selection term” is (1) a term that specifically identifies a person, account, address, or personal device, or any other specific identifier; and (2) is used to limit, to the greatest extent reasonably practicable, the scope of tangible things sought consistent with the purpose for seeking the tangible things. In the case of “call detail records,” a specific selection term “means a term that specifically identifies an individual, account, or personal device.”
[6] If the application’s statement of facts shows that the tangible things sought relate to (i) a foreign power or an agent of a foreign power; (ii) the activities of a suspected agent of a foreign
power who is the subject of an authorized investigation; or (iii) an individual in contact with, or known to, a suspected agent of a foreign power who is the subject of such an authorized investigation, the tangible things being sought by the application are presumptively relevant to that authorized investigation.
[7] 50 U.S.C. § 1801(a)(4) specifically includes in the definition of a “foreign power” “a group engaged in international terrorism or activities in preparation therefor.”
[8] See, e.g., 50 U.S.C. §§ 105(i), 501(e), and 702(i)(3) (“immunity” provisions to third parties providing assistance in the execution of FISA orders).
[9] See 50 U.S.C. § 1861(c)(2)(F) (providing that, in the case of an application seeking production of call detail records relating to an international terrorism investigation, the government may seek the prompt production of two sets of related call detail records).
[10] A description of NSA’s implementation of the USA Freedom Act is found in Transparency Report: The USA Freedom Act Business Records FISA Implementation, NSA Civil Liberties and Privacy Office (January 15, 2016) available at http://www.nsa.gov.
[11] All statistics presented in the tables that follow are drawn from the Statistical Transparency Report Regarding Use of National Security Authorities – Calendar Year 2017 issued by the Office of the Director of National Intelligence (Office of Civil Liberties, Privacy and Transparency), April 2018 (available at http://dni.gov).
[12] Certain caveats relating to the statistics presented are included in the Statistical Transparency Report and should be noted. Illustrative is how the Intelligence Community counts FISA business record statistics. Assume that in 2017, for example, the government submitted a business records request targeting “John Doe” using email addresses john.doe@serviceproviderX, john.doe@serviceproviderY, and john.doe@serviceproviderZ as selectors. Assume, further, that a FISC order was issued directing service providers X, Y, and Z to produce business records and that each provider returned 10 non-targeted email addresses that were in contact with the target. Based on this scenario, the DNI would report the following statistics: (a) one order by the FISC for the production of tangible things (i.e., business records), (b) one target of said order, and (c) 33 unique identifiers representing the 3 targeted email selectors and the 30 non-targeted email addresses in contact with those selectors.
[13] 50 U.S.C. §§ 1809(a) and 1810.
[14] 50 U.S.C. § 1805(c)(2)(B).
[15] See, Electronic Communications Privacy Act of 1986, P.L. 99-508, § 106(d)(3), codified at 18 U.S.C. § 2518(11).
[16] The governing FISA provisions are found at 50 U.S.C. §§ 1804(a)(2), 1805(c)(1)(A).
[17] Id.
[18] See, 18 U.S.C. §§ 2518(11)(a), 2518(12).
[19] Those “secondary” issues are addressed by determining, for example, whether a FISA application contains sufficient facts to establish probable cause that the identified communications facility is being used by a foreign power or an agent of a foreign power (see, e.g., 50 U.S.C. § 1805(a)(2)(B)), or that the records sought are related to an investigation to obtain foreign intelligence information or to protect against international terrorism or clandestine intelligence activities. See, e.g., 50 U.S.C. § 1861(b)(2)(B).
[20] 50 U.S.C. § 1801(b)(1)(C).
[21] Id.
[22] Charlie Savage, “N.S.A. Purges Hundreds of Millions of Call and Text Records,” New York Times, June 29, 2018.
[23] Recall that, in the DNI’s Statistical Transparency Report for CY 2017, the DNI acknowledges that NSA lacks the technical capability of isolating unique identifiers so that its metric for counting the number of unique identifiers is necessarily “over-inclusive.” How “over-inclusive” remains a question eluding an answer.
[24] Suzanne Spaulding, If it ain’t broke, don’t fix it, Patriot Debates: Experts Debate the USA Patriot Act (Stewart Baker and John Kavanaugh, Editors), American Bar Association Standing Committee on Law and National Security, July 2005.
[25] George Croner, “The Clock is Ticking: Why Congress Needs to Renew America’s Most Important Intelligence Collection Program,” FPRI E-Notes, September 29, 2017.